Introduction
I would like to use this chance to extend my gratitude and give thanks to the Internet Society for giving this training. I have had the privilege to be part of the Global Volunteer Training Program 2020, under the Internet Routing Security, MANRS Group C.
These blog serve as a chapter initiative; a means of sharing knowledge I have acquired during the ISOC Program Training. Content of this blog is a brief summary of the training with text extracted from different resources that have been made available during the training.
Internet Routing
Routing is the practice of determining the way to get data from one location to another location over a network or multiple networks. At its core, the routing system is built on trust among networks. The global routing system is a complex, decentralized system made up of tens of thousands of individual networks. Independent business decisions and trusted relationships between individual network operators implementing the Border Gateway Protocol (BGP) determine how the network operates. The meshed system’s architecture contributes to its resilience, scalability, and ease of adoption.
However, internet routing foundation has incidents affecting the routing system. The incidents are Border Gateway Protocol updates that have negative impact such as route hijacking, route leaks, IP spoofing and many other harmful activities.
MANRS
The Mutually Agreed Norms for Routing Security (MANRS) is a set of visible, baseline practices for network operators to improve the security of the global routing system. In 2014, a group of likeminded network operators developed MANRS as a voluntary initiative. MANRS improves the security and reliability of the global routing system, based on collaboration among participants and shared responsibility for the internet infrastructure. It defines four simple but concrete actions for network operators to implement to greatly improve Internet security and reliability:
- Filtering
- IP source Validation (Anti-spoofing)
- Coordination
- Global Validation
The first two improvements (filtering and IP source validation) address the root causes of common routing incidents. The second two, (coordination and global validation) help limit the impact of incidents and decrease the likelihood of future incidents.

Filtering
The act of preventing propagation on incorrect routing information. It is achieved by network operator defining a clear routing policy and implement a system that ensures correctness of their own announcements and announcements from customers to adjacent networks with prefix and AS-path granularity. Network operator take reasonable steps when checking the correctness of its customer’s announcements to ensure that the customer legitimately holds the ASN and address space it announces.
Two levels of filtering:
- Prefix-level filtering
Used to secure inbound routing advertisement particularly from customer networks and outbound announcements to non-customer peers.
- AS-path filtering
Used to require the customer network to be explicit about which autonomous systems are downstream of that customer to prevent route leaks.
Building filters
Before building filters, it is important to apply due diligence and check whether the information provided by the customer about their identity and resources are correct. To determine whether the customer really hold the ASN being filtered, identity of that particular ASN have to be verified.
Ways to build filters:
- Use Internet Routing Registries (IRR) and require the customers to register route objects
- Use Resource Public Key Infrastructure (RPKI) and require customers to create Route Origin Authorization (ROA).
- Use internal database with the information provided as part of the provisioning process.
Internet Routing Registries (IRR)
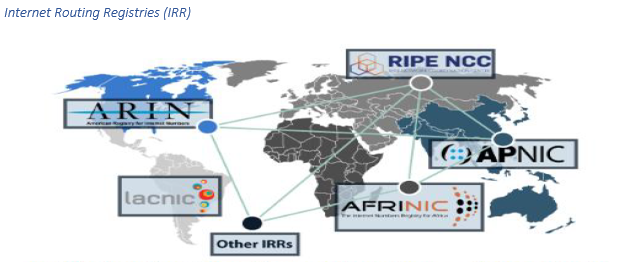
These are central places where routing information is published. They document ASNs with IP addresses they announce and policies for exchanging routes between ASNs. All IRRs are authorized against authoritative sources.
Prefix filters using IRR:
- Specific-prefix outbound filtering of a network to peers and upstream (required)
- Specific-prefix inbound filtering from customer (required)
- Specific-prefix inbound filtering of peers to a network (recommended)
Prefix filter configuration tools:
- BGPQ3 – A prefix-list generator.
- IRRToolset – A router configuration template processor.
Routing Public Key Infrastructure (RPKI)
It allows validating route announcements the same way as the IRR. However, in RPKI, operators register their announcements in the form of ROAs which are then used by operators to either generate filters or validate announcements using advanced techniques like RPKI-to-router protocol.
Anti-spoofing
It is a way of preventing traffic with spoofed source IP addresses. It enables source address validation for at least single-homed stub customer networks, their own end-users and infrastructure. Network operators implements a system with anti-spoofing filtering to prevent packets with an incorrect source IP address form entering and leaving the network.
Anti-spoofing techniques
- Access Control Lists (ACL)
- Unicast Reverse Path Forwarding (uRPF)
- Aggregation points
- IP verify source
ACLs
ACLs are used to filter traffic by controlling whether routed packets are forwarded or blocked at the router’s interfaces. They are configured to allow specific address range and deny all others. ACLs are commonly deployed on the Provider Edge (PE) or Customer Edge (CE).
uRPF
The concept behind uRPF is that the traffic from known invalid networks should not be accepted from which they should not have originated. It enables routers to verify the reachability of the source address in packets being forwarded.
uFPF modes:
- Strict mode
In strict mode each incoming packet is tested against the FIB (Forwarding Information Base) and if the incominginterface is not the best reverse path the packet check will fail.
- Loose mode
In loose mode each incoming packet’s source address is tested against the FIB. The packet is dropped only if the source address is not reachable via any interface on that router
- Feasible mode
In feasible mode, the FIB maintains alternate routes to a given IP address. If the incoming interface matches with any of the routes associated with the IP address, then the packet is forwarded. Otherwise the packet is dropped.
Aggregation points
When ACLs at the PE/CE boundary are not possible, filtering at an aggregation point is the second-best solution. Ingress filtering at the aggregation router allows only packets with source IP address from the customer networks to be aggregated, this limits the spoofing possibilities for the group of customers to a small range of address.
IP verify source
Ethernet networks are broadcast domains, and by default there is no validation of who is allowed to send packets with which addresses. To verify source addresses used by the connected devices, the “ip verify source” setting is used.
The three variants of this feature include:
- IP verify source – verifies the source address
- IP verify source port-security – verifies the source MAC address
- IP verify source tracking port-security – tracks the binding between IP addresses and MAC addresses.
Coordination
Facilitating global operational communication and coordination between network operators. This maintain globally accessible up-to-date contact information in common routing databases. Network operators are advised to maintain their contact data in common places, objects registered in the regional databases and their public websites. The databases to publish and maintain operators contact information include Whois database, IRR database and peering-DB. Since Internet Routing Registries are used to validate routing information, keeping contact information for those objects up-to-date is very important.

Global Validation
Facilitating validation of routing information on a global scale. This is achieved by network operators publicly publishing routing policy, ASNs and prefixes that are intended to be shared and validated by others as discussed in above sections.
Importance of MANRS
- MANRS improves the economic incentives for routing security by allowing network operators to signal their routing security posture to customers, competitors and policymakers.
- It also provides metrics for measuring routing security.
- MANRS measurements can serve as a valuable 3rd party assessment of a network operator’s security practices.
Joining MANRS (as a link to the joining page)
Reference
MANRS-Ambassador-Presentation
MANRS-BCOP-20170125
Routing-Security-for-Policymakers-EN
Article by: Lucas Chihinga Tjimango
Right here is the perfect website for anyone who hopes to understand this topic. You realize so much its almost hard to argue with you (not that I personally would want to…HaHa). You definitely put a brand new spin on a subject which has been discussed for years. Great stuff, just wonderful!
Thanks for the various tips provided on this website. I have noticed that many insurance agencies offer buyers generous deals if they prefer to insure several cars with them. A significant volume of households have got several motor vehicles these days, particularly those with mature teenage kids still residing at home, as well as the savings upon policies can soon increase. So it is a good idea to look for a great deal.